OCI Zero Trust Packet Routing (ZPR)
Understanding the Concepts Behind Oracle’s Modern Security Architecture
Ahmed Hassan
5/6/20263 min read


Decoupling Policy from Infrastructure: How Zero Trust Packet Routing Works
Zero Trust has evolved from a foundational cloud security principle into a granular networking reality.
Oracle Cloud Infrastructure (OCI) Zero Trust Packet Routing (ZPR) takes this concept to the packet level by decoupling security policy from the underlying network architecture.
Unlike traditional perimeter-based defenses, OCI ZPR operates on a "deny-by-default" architecture where every connection is untrusted until verified. By utilizing an intent-based policy language and security attributes, administrators can define specific data access pathways that remain independent of IP addresses or VCN configurations. The result is a simplified, audit-ready environment where traffic is only permitted if it explicitly aligns with your security intent.
What Is Zero Trust Packet Routing?
Traditional cloud networks assume that anything inside the VCN is safe. Attackers exploit this by gaining access to a single machine and moving laterally within the network.
ZPR changes this completely
No traffic is trusted — even if it comes from inside the VCN
Each packet is inspected based on identity, attributes, and context
Routing decisions are enforced per packet
Network paths follow explicit allow rules, not implicit trust
Segmentation becomes fine-grained, dynamic, and policy-driven
simply:
“Every packet must prove its legitimacy before being routed.”
It is not just network segmentation — it is identity-driven packet-level verification.
Why ZPR Matters?
Modern threats commonly target:
Weak internal trust
Broad subnet-level access
Flat networks
Shared internal credentials
Misconfigured firewalls
ZPR eliminates these risks by embedding Zero Trust at the network layer.
Key advantages
Eliminates lateral movement
Tightens segmentation without complexity
Ensures workloads can communicate only when allowed
Reduces blast radius of any breach
Protects east-west (internal) traffic, not just north-south
ZPR is crucial for regulated industries, multi-tier applications, and confidential workloads.
How Zero Trust Packet Routing Works in OCI
ZPR enforces security using three core principles:
1- Identity-Based Routing
Instead of routing based only on source and destination IP addresses, OCI considers:
Instance identity
Workload identity
Policy attributes
Service-level permissions
This creates an “identity fingerprint” for the traffic Even if an attacker spoofs an IP, they cannot spoof identity.
2- Default Deny Model
In ZPR:
No communication is allowed unless explicitly permitted.
Everything starts as blocked, You grant access per application, per direction, and per identity pair.
Examples:
App Server → DB Server (allowed)
Monitoring Agent → Metrics Service (allowed)
App Server → Another App Server (denied unless specified)
No hidden paths. No accidental access.
3- Application-Centric Policies
Traditional network firewalls force you to think in terms of:
IP addresses
Port numbers
Subnets
ZPR policies let you think in terms of:
Applications
Services
Workload groups
Identities
Compartments
Tags
This makes policies cleaner, easier to maintain, and more secure.
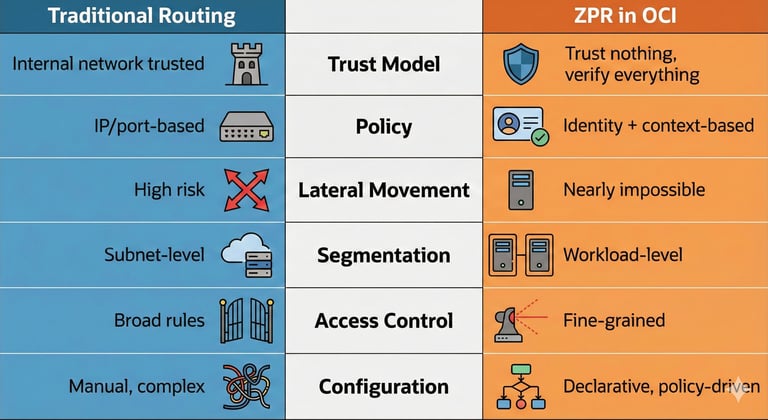
ZPR Compared to Traditional Routing
ZPR shifts focus from network boundaries to workload identities.
Where ZPR Applies Inside OCI
Zero Trust Packet Routing protects:
East–West Traffic, Between
Compute instances
Application tiers
Microservices
Kubernetes nodes
Databases
Containers
North–South Traffic, When integrated with:
OCI Network Firewall
OCI WAF
OCI Load Balancing
API Gateway
VCN-to-VCN Traffic, Through:
Local peering
Remote peering
DR networks
ZPR enforces policy consistently across the entire OCI network fabric.
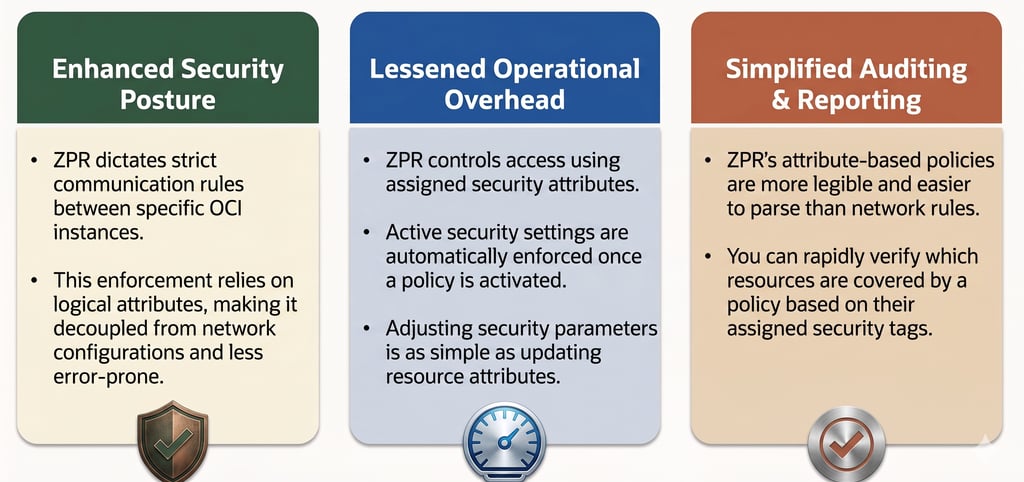
ZPR Enforces “No Human Error” Security
A large percentage of security breaches come from misconfiguration:
Incorrect security lists
Overly permissive ports
Broad subnet rules
ZPR solves this by:
Enforcing explicit-only routing
Binding traffic to workload identity
Blocking communication if any attribute mismatches
Preventing unintended paths automatically
This creates a more deterministic, safer environment.
ZPR in Zero Trust Architectures
ZPR is a core building block for Zero Trust architectures, enabling:
Micro-segmentation
Service isolation
Dynamic, identity-aware routing
Complete elimination of implicit trust
When combined with services like:
OCI Bastion (JIT access)
OCI Network Firewall (deep inspection)
IAM + Tags (identity governance)
Cloud Guard (continuous monitoring)
Conlusion
Zero Trust Packet Routing (ZPR) is one of the most innovative and impactful security features in OCI. By evaluating identity and context at the packet level, ZPR ensures that workloads communicate only when explicitly permitted — greatly reducing the risk of lateral attacks and misconfigurations.
ZPR is more than a feature, it is a fundamental shift in how secure networking is done in the cloud. For any architecture aiming to adopt Zero Trust principles, ZPR should be a core component.
Get in Touch
ah.hassan09@gmail.com
© 2025. All rights reserved.
Stay Updated
Get the latest posts on OCI and cloud tech
Terms and Conditions
