OCI Security Services
Building a Secure Cloud Foundation
Ahmed Hassan
5/4/20265 min read

Building a Secure Cloud Foundation using OCI Security Services
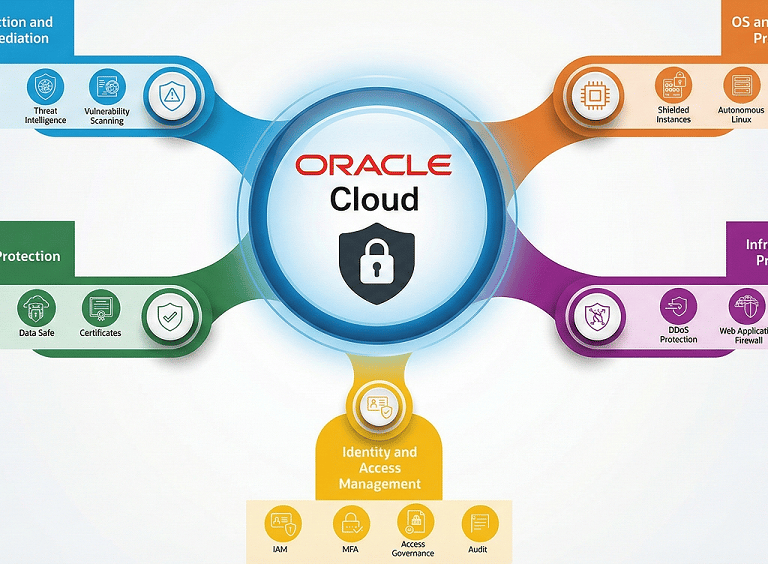
Security is one of the most important responsibilities for any organization operating in the cloud. Oracle Cloud Infrastructure (OCI) adopts a defense-in-depth strategy, embedding security at every layer from identity and access control to network protection, workload isolation, data security, and continuous monitoring.
In this series, we’ll walk through the major OCI security services, explain how they work together, and highlight the value they provide when designing secure cloud architectures.
Defense-in-Depth in OCI
OCI embeds security at multiple layers of its stack. Instead of thinking about security as a single tool or feature, OCI provides a collection of integrated services across these domains:
Identity and Access Management
Infrastructure and Network Protection
Operating System & Workload Protection
Data Protection & Encryption
Detection, Response & Posture Management
This layered approach ensures that even if one guardrail fails, several others remain in place to protect your environment.
1. Identity & Access Management
Security starts with controlling who can access what. OCI provides a mature set of IAM capabilities to make this easy and secure.
OCI IAM
Cloud-native identity platform that manages users, groups, and policies to control who can access which OCI resources and what actions they can perform and handles:
Authentication (passwords, API keys, certificates)
Authorization (policies defining what actions are allowed)
Auditing (visibility into every API call)
And has some many Key Features like:
MFA: Adds extra verification layers.
Federation: Integrates with Microsoft AD, Okta, and other SAML providers.
Access Governance: Automates provisioning and monitors permissions for anomalies.
Audit Service: Captures all API calls for compliance and forensics.
Strong IAM is the foundation of every OCI deployment.
2. Infrastructure Protection
OCI provides several native tools to block attacks and secure network boundaries.
DDoS Protection
OCI provides always-on network-level protections that absorb and filter volumetric and protocol-based DDoS attacks before they reach tenant workloads.
These controls are built into the edge and core networking fabric, reducing downtime risk without requiring you to deploy separate DDoS appliances.
Layer 3/4: Automatically built into the OCI network no configuration needed
Layer 7: Handled by OCI Web Application Firewall (WAF).
Network Security Controls
Security Lists
Security Lists act as virtual firewalls at the subnet level, defining stateful ingress and egress rules based on source/destination, protocol, and port.
They provide coarse-grained packet filtering for all instances in a subnet, useful for baseline network controls and simple architectures.
Network Security Groups
Network Security Groups apply virtual firewall rules directly to VNICs, enabling instance-level segmentation within the same subnet.
They support stateful rules like Security Lists but allow finer-grained isolation per application or tier, independent of subnet boundaries.
OCI Network Firewall
Fully managed, next-generation firewall (powered by Palo Alto Networks) service that inspects traffic from layer 3 to layer 7 with stateful filtering, IDS/IPS, and URL/FQDN filtering.
You can route VCN, internet, and on‑prem traffic through it to enforce centralized policies, TLS inspection, and advanced threat protection at scale.
A next-generation cloud-native firewall offering:
Intrusion detection & prevention
URL filtering
Threat intelligence
Encrypted traffic inspection
This service provides deep packet inspection and robust protection from both known and unknown threats.
3. Operating System & Workload Protection
OCI also provides mechanisms to secure compute instances before and after provisioning.
Shielded Instances
Compute shapes that add secure boot and firmware protections to help ensure only trusted, signed OS images run on the VM.
They provide stronger resistance to boot‑level malware and tampering by validating the platform and image integrity at startup.
Main Features:
Secure Boot
Measured Boot
Trusted Platform Module (TPM)
These protect system integrity and prevent unauthorized bootloaders.
Autonomous Linux
Self-patching Oracle Linux image that automatically applies OS and kernel updates without downtime using Ksplice technology.
It reduces operational overhead and security exposure windows by continuously keeping the OS up to date with the latest fixes.
OCI’s self-patching Linux distribution:
Automatic kernel updates
Automatically optimized for performance
Fully RHEL-compatible
OCI Bastion
Managed, time-bound, and IP-restricted access service for private resources using browser-based SSH or RDP, without exposing public IPs, essential for Zero Trust environments.
It replaces traditional jump hosts by brokering audited, just-in-time access to compute instances in private subnets.
OS Management
Service for tracking and automating OS package updates, patches, and configuration compliance across your compute fleet.
You can schedule patching, monitor update status, and standardize OS baselines to reduce vulnerabilities and drift.
4. Data Protection & Encryption
Data encryption isn’t optional anymore—it’s a fundamental requirement. OCI includes several native tools to secure data at rest and in transit.
OCI Vault Service
Centralized key and secret management service that stores keys in hardware security modules and exposes them via APIs for encryption operations.
It lets you manage lifecycle, rotation, and access control for keys, passwords, and certificates used by OCI services and custom apps.
Dedicated & External KMS
Dedicated KMS: Provides a tenant-isolated key management instance with dedicated HSM resources for stricter regulatory and sovereignty requirements.
Gives more control over key tenancy and performance while integrating with the same OCI encryption and data protection services.
External KMS: Enables OCI services to use encryption keys hosted in an external key manager you control, such as on-prem HSMs or third-party KMS.
This lets you enforce “hold your own key” models and centralized governance while still leveraging OCI-native encryption.
Data Safe
Cloud security service that discovers, assesses, and monitors sensitive data in Oracle databases on OCI and elsewhere.
It offers user risk analytics, activity auditing, and data masking to reduce insider risk and improve database compliance posture.
OCI Certificates
Managed service for provisioning, storing, and automatically renewing TLS certificates for workloads running on OCI.
Helps prevent outages and security issues from expired certs by centralizing lifecycle management and integrating with OCI services.
5. Detection, Response & Posture Management
Security is not a one-time activity. Continuous monitoring is critical.
Cloud Guard
Cloud-native posture management service that continuously monitors OCI resources for:
Misconfigurations
Risky activity
Security risks
It generates problems and can trigger responder recipes to automatically remediate common security and compliance issues.
Security Zones
Predefined policy frameworks that enforce strict security rules in selected compartments, such as Mandatory encryption or No public subnets.
Resources that violate zone policies are blocked or flagged, making it easier to enforce secure-by-default environments.Perfect for regulated workloads.
Threat Intelligence
Service that curates threat feeds with malicious IPs, domains, and other indicators for use in OCI security policies and detections.
Integrating this data with services like Cloud Guard and Network Firewall improves detection of known bad actors targeting your tenancy.
Aggregates threat data from global feeds to identify:
Malicious IPs
Malware hosts
Command and control domains
Vulnerability Scanning
Service that regularly scans compute instances and container images for OS and application vulnerabilities and missing patches.
Scan results can be prioritized and integrated into remediation workflows to reduce exposure to exploitable weaknesses
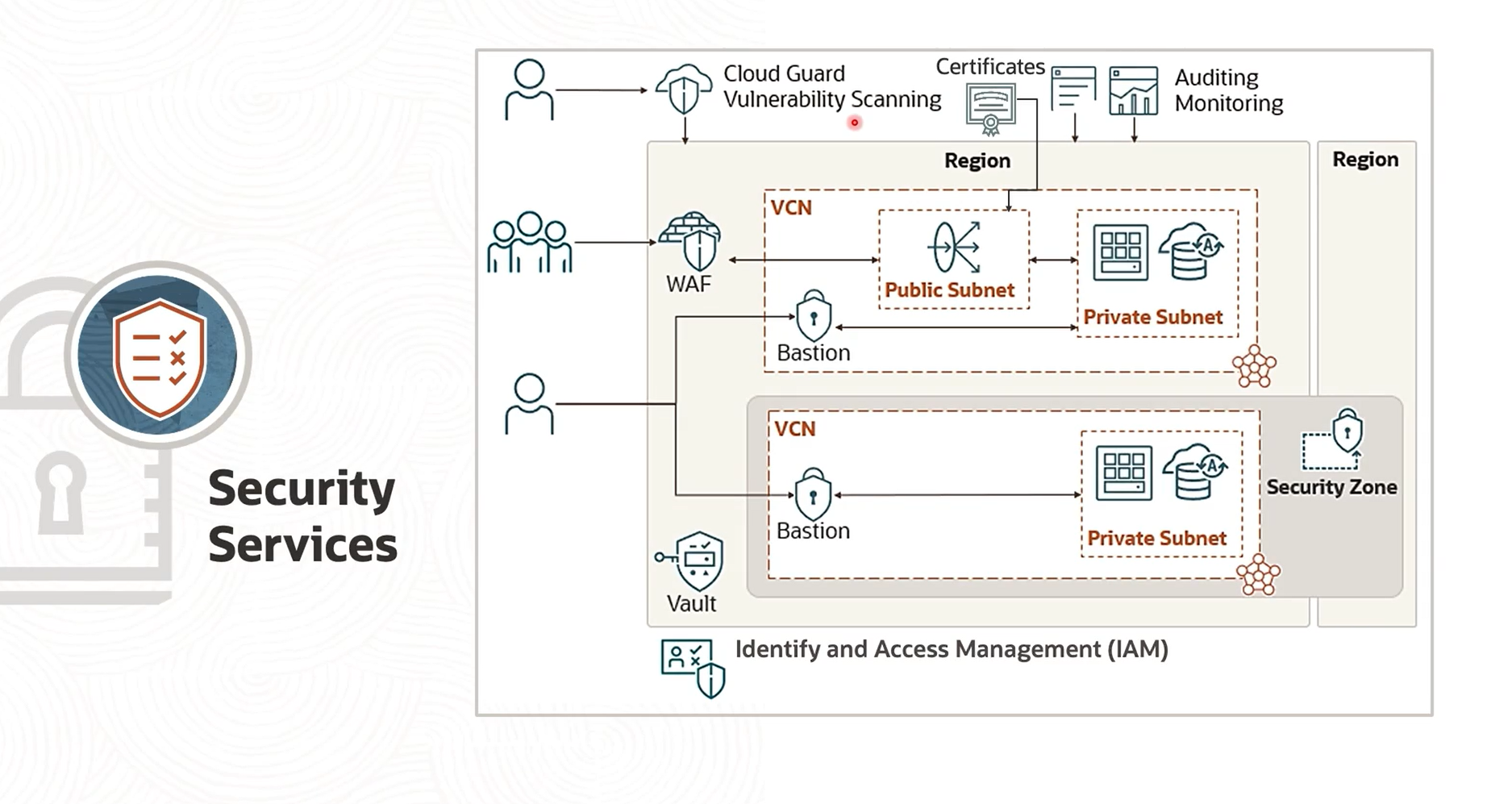
Bringing It All Together
Imagine an application hosted in OCI:
The VCN is controlled by NSGs and Security Lists.
WAF protects from layer-7 attacks.
Bastion provides controlled access to private compute instances.
IAM policies ensure only the right users have permissions.
Vault manages encryption keys for Object Storage and databases.
Cloud Guard monitors the environment continuously.
Objects in Object Storage are encrypted by default, with options for customer-managed keys.
This integrated model delivers a comprehensive and modern cloud security posture.
Conclusion
OCI offers a rich suite of security services that work together to protect applications, data, and infrastructure at every layer. Whether your priority is identity, network protection, data encryption, or continuous monitoring, OCI provides tools built with a security-first mindset.
Understanding these services is the first step toward designing a secure and scalable cloud architecture.

Get in Touch
ah.hassan09@gmail.com
© 2025. All rights reserved.
Stay Updated
Get the latest posts on OCI and cloud tech
Terms and Conditions
